// Cyber Asset Attack Surface Management (CAASM)
Identify exposure gaps and reduce attack surface risk
Cyber Asset Attack Surface Management (CAASM) consolidates and contextualizes cyber asset data across on-premises, cloud, SaaS, and identities. The goal is a unified, up-to-date view of what exists, what is exposed, and where coverage gaps create risk, so security and IT can act with confidence.
// Discover to Manage
Cyber Asset Attack Surface Management: Discover. Assess. Secure.
CAASM with Raynet One: visibility you can act on, powered by ITAM-native context
With every new technology, the number of cyber assets grows, often unnoticed. Shadow IT, missing visibility, and siloed data sources create gaps attackers can exploit and teams struggle to close.
Raynet One brings asset intelligence from existing systems into one inventory you can use in practice. It reconciles asset data from ITAM, CMDB, cloud platforms, and security tools into one inventory, then enriches it with ITAM-grade context such as ownership, environment, and business relevance. This helps teams trust what exists, spot control coverage gaps faster, and route findings to the right owners without guesswork.
How you stay in control:
Identify and assess cyber assets and exposure gaps with a unified inventory, consistent context, and audit-ready reporting.

// Your benefits at a glance
Strengthen cyber resilience with contextualized asset intelligence
Asset visibility
Gain a centralized view of cyber assets across on-premises, hybrid, and cloud, including SaaS and identities, to reduce blind spots and improve coverage.
Coverage gaps
See where security tools are working reliably and where they are not, so gaps can be addressed before they become incidents.
Faster response
Link assets to exposure signals and context so security and IT can prioritize investigations, assign ownership, and coordinate remediation more efficiently.
Audit readiness
Maintain a consolidated, up-to-date asset foundation for governance, reporting, and security reviews, with traceable context across systems.
Cyber Asset Attack Surface Management with Raynet One
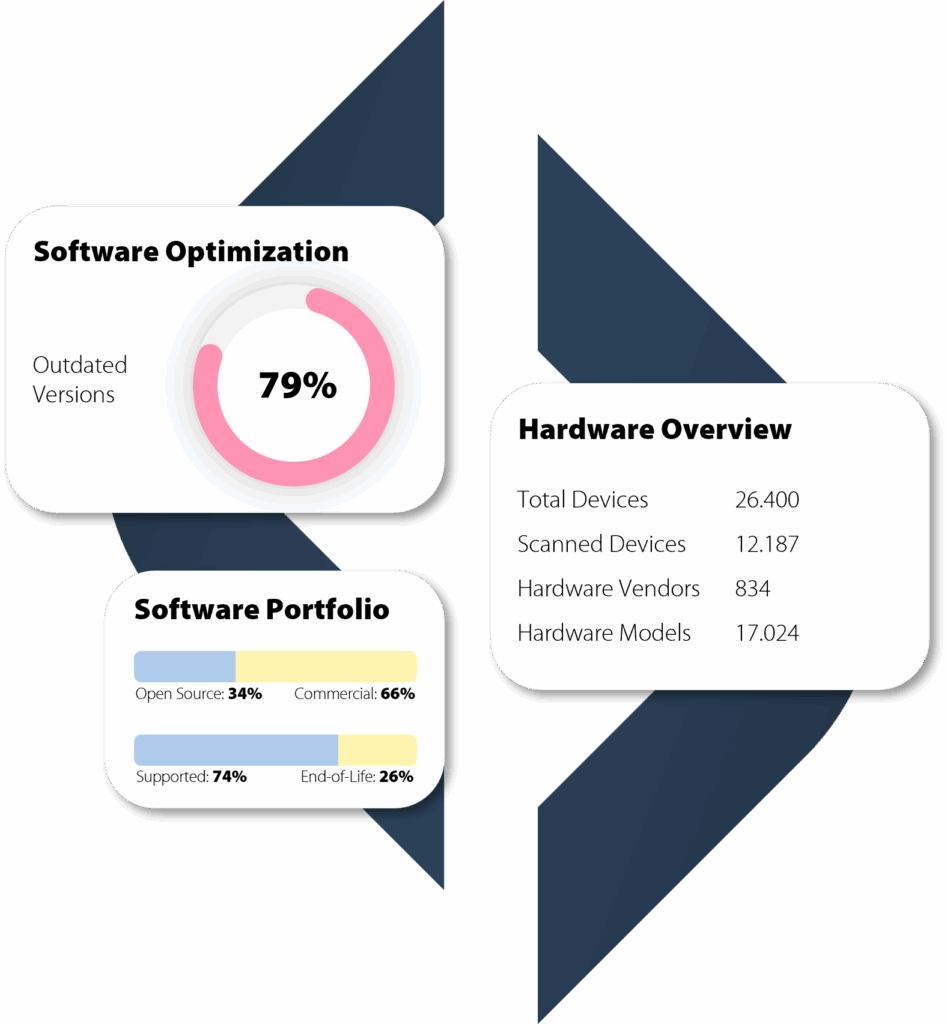
You can only protect what you can see. Raynet One identifies cyber assets across your environment, from servers, endpoints, and IoT devices to applications, services, databases, cloud workloads, SaaS, and digital identities such as user accounts and roles.
The result is a complete, centralized overview of your attack surface that is immediately actionable. Instead of isolated tool outputs, you get a trusted asset foundation enriched with the context security teams need, including ownership, location, environment, and business relevance.
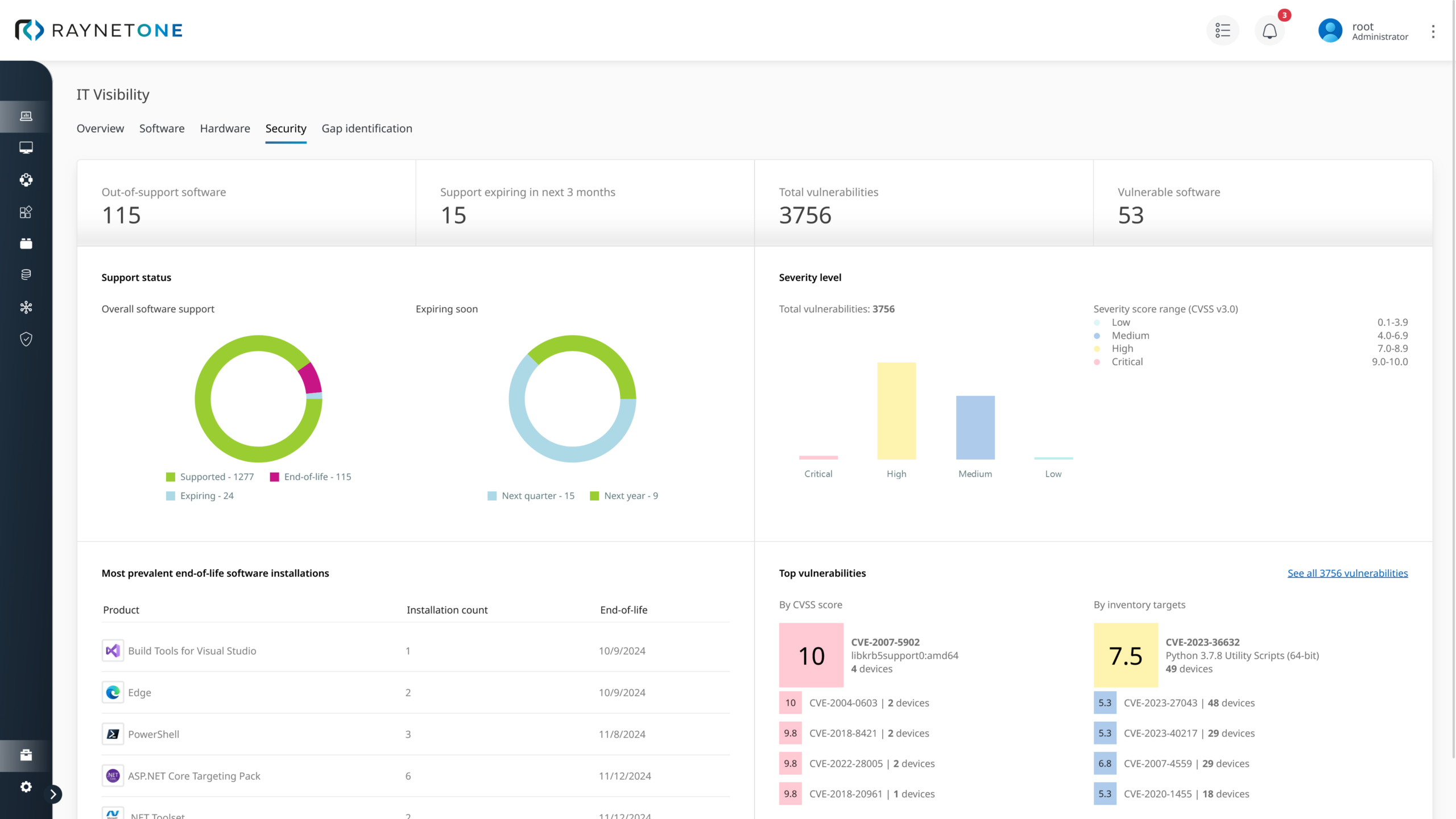
Raynet One also shows where protection is strong and where it is missing. You can see unmanaged systems, gaps in security control coverage, and which exposure signals threaten the stability, compliance, and availability of your business processes. This creates a reliable basis for incident response, governance, and a proactive security strategy.
Cyber attack stopped. Complete IT transparency with Raynet in just 13 days.

An international retail group became the target of a severe phishing attack. Within hours, large parts of the IT infrastructure went down, the situation was critical.
With Raynet One the company gained immediate transparency over all affected cyber assets and was able to close security gaps in a targeted way.
After just 13 days, the entire IT environment was fully restored, more secure, more transparent, and future-ready.
Customers who rely on Raynet technologies








Integrate CAASM with the systems you already run
CAASM only works when it is connected to your real environment. Raynet One consolidates and reconciles asset intelligence from existing IT and security systems to reduce blind spots, clarify control coverage, and support faster investigations.
Raynet One connects to sources such as:
- ITAM and CMDB systems to establish a trusted asset baseline with ownership and lifecycle context
- Cloud platforms and cloud security tooling to capture cloud workloads, configurations, and exposure signals
- SaaS applications to uncover shadow IT usage and unapproved subscriptions
- Identity providers and directories to include users, accounts, roles, and access relationships
- Vulnerability management tools to link exposure signals to real assets and environments
- Endpoint and UEM platforms to correlate devices and management status across the estate
- Security telemetry and control systems to understand where protection is applied and where it is missing
This creates a queryable attack surface view that supports faster investigations, clearer ownership routing, and audit-ready reporting, without becoming another passive reporting layer.
Discover exciting topics related to Cyber Asset Attack Surface Management
Frequently asked questions about Cyber Asset Attack Surface Management
What is Cyber Asset Attack Surface Management (CAASM)?
Cyber Asset Attack Surface Management consolidates and contextualizes cyber asset data across environments and systems. The goal is to make the full attack surface visible, identify blind spots and coverage gaps, and reduce risk through a trusted, unified inventory.
What are the benefits of CAASM for businesses?
Who can benefit from Cyber Asset Attack Surface Management?
How does CAASM differ from traditional Vulnerability Management?
By analyzing and consolidating identical applications, license types, or overlaps, organizations can streamline their software portfolio. This leads to measurable reductions in software costs and more efficient use of resources.
How does CAASM relate to Continuous Threat Exposure Management (CTEM)?
It is particularly valuable for CIOs, CTOs, SAM managers, IT directors, and security and compliance leaders in organizations with complex IT landscapes. They require a centralized data foundation to manage risks and successfully drive strategic IT initiatives.
How quickly can CAASM be implemented with Raynet One?
With Raynet One, organizations receive an initial meaningful overview of their entire IT landscape within just a few minutes. The solution is quick to implement, scalable, and ready to use immediately.
Contact our experts
Interested in our solutions, need further Information, or have questions?
With more than 25 years of experience and numerous customer projects worldwide, we can help you with your challenges – contact us today!